Okta
Overview
This guide provides steps to integrate Okta with ID.me using the SAML 2.0 protocol.
Intended audience
Developers and IAM administrators responsible for configuring federation between Okta and ID.me.
What you will build
A federated authentication flow where Okta delegates user authentication to ID.me.
Result
A federated SAML authentication flow where Okta delegates authentication to ID.me.
Identity proofing behavior
Authentication behavior, identity verification settings, and returned attributes are driven by ID.me policy configurations.
Authentication flow
The following steps outline the SAML authentication flow between the user, Okta, and ID.me:
Prerequisites
- An Okta Developer Account (sign up at
https://developer.okta.com/signup/) - Administrator access to the Okta tenant
- An ID.me sandbox account for testing your integration
- Understanding of SAML flows and terminology
Environments
ID.me provides two environments:
https://api.idmelabs.com/
https://api.id.me/
All ID.me OIDC and SAML endpoints are derived from the base URL above. For production, replace the sandbox base URL in every ID.me endpoint you configure.
Examples
- OIDC issuer (Sandbox):
https://api.idmelabs.com/oidc - OIDC issuer (Production):
https://api.id.me/oidc - SAML metadata URL (Sandbox):
https://api.idmelabs.com/saml/metadata - SAML metadata URL (Production):
https://api.id.me/saml/metadata
Configure Okta
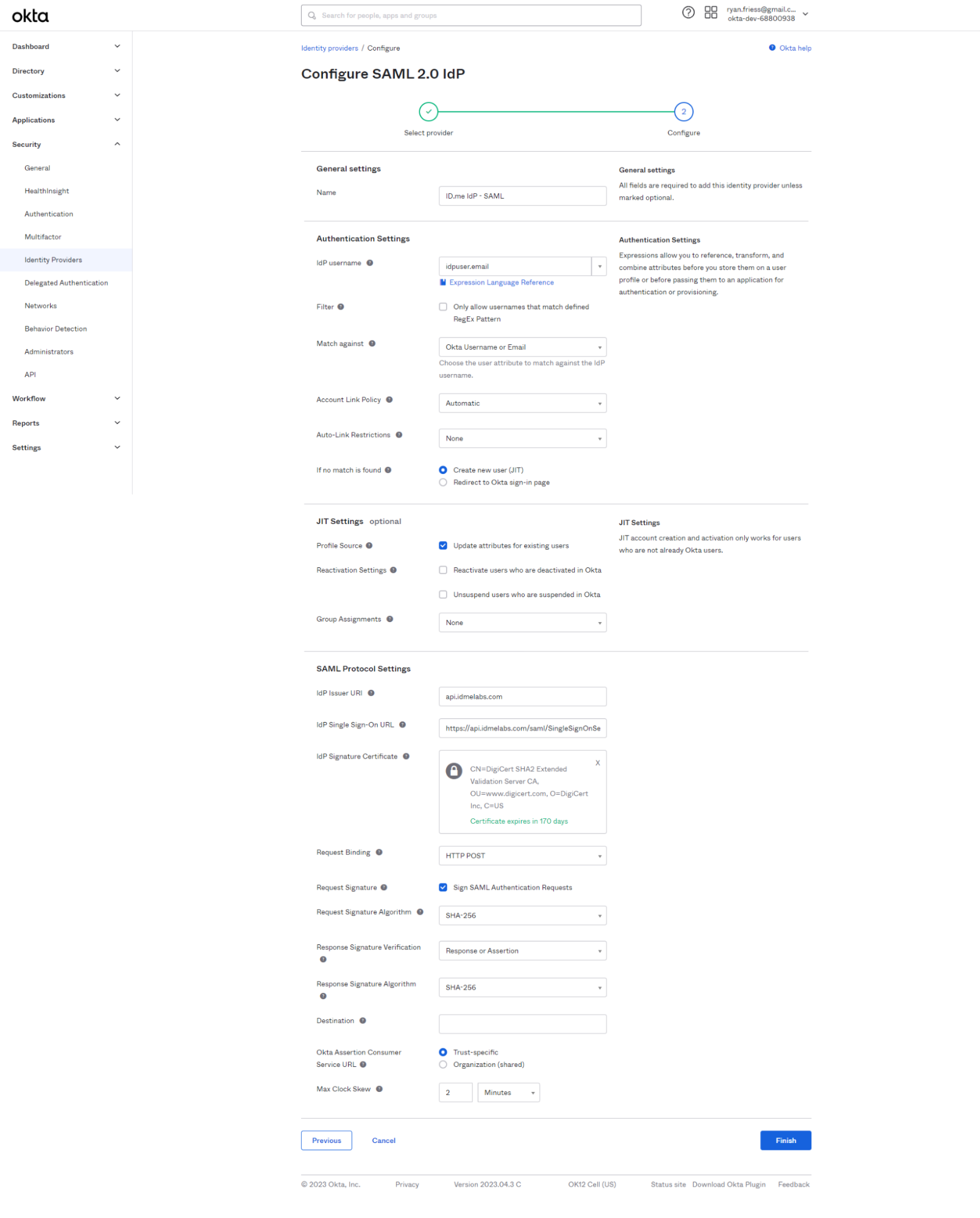
Create an Identity Provider
Configure the User Matches:
- IdP Username:
idpuser.email - Match against:
Okta UsernameorEmail - Account Link Policy:
Automatic
Configure the JIT Settings:
- If no match is found:
Create New User (JIT) - Profile Source:
Update attributes for existing users
Configure the SAML Protocol Settings:
To obtain the ID.me Signing Certificate, download the metadata from https://api.idmelabs.com/saml/metadata/provider. Copy the X.509 certificate between the ds:X509Certificate tags. You may need to format it as a PEM file with standard headers using a tool like SAMLTool.
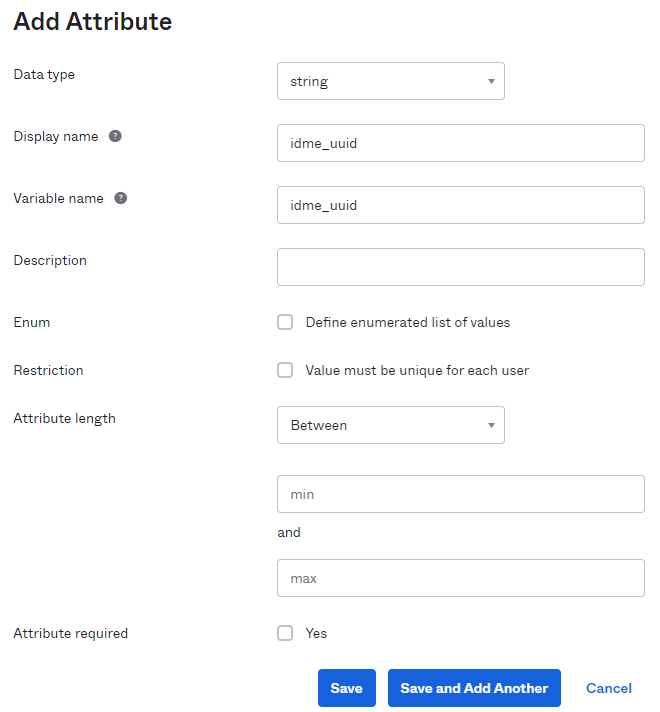
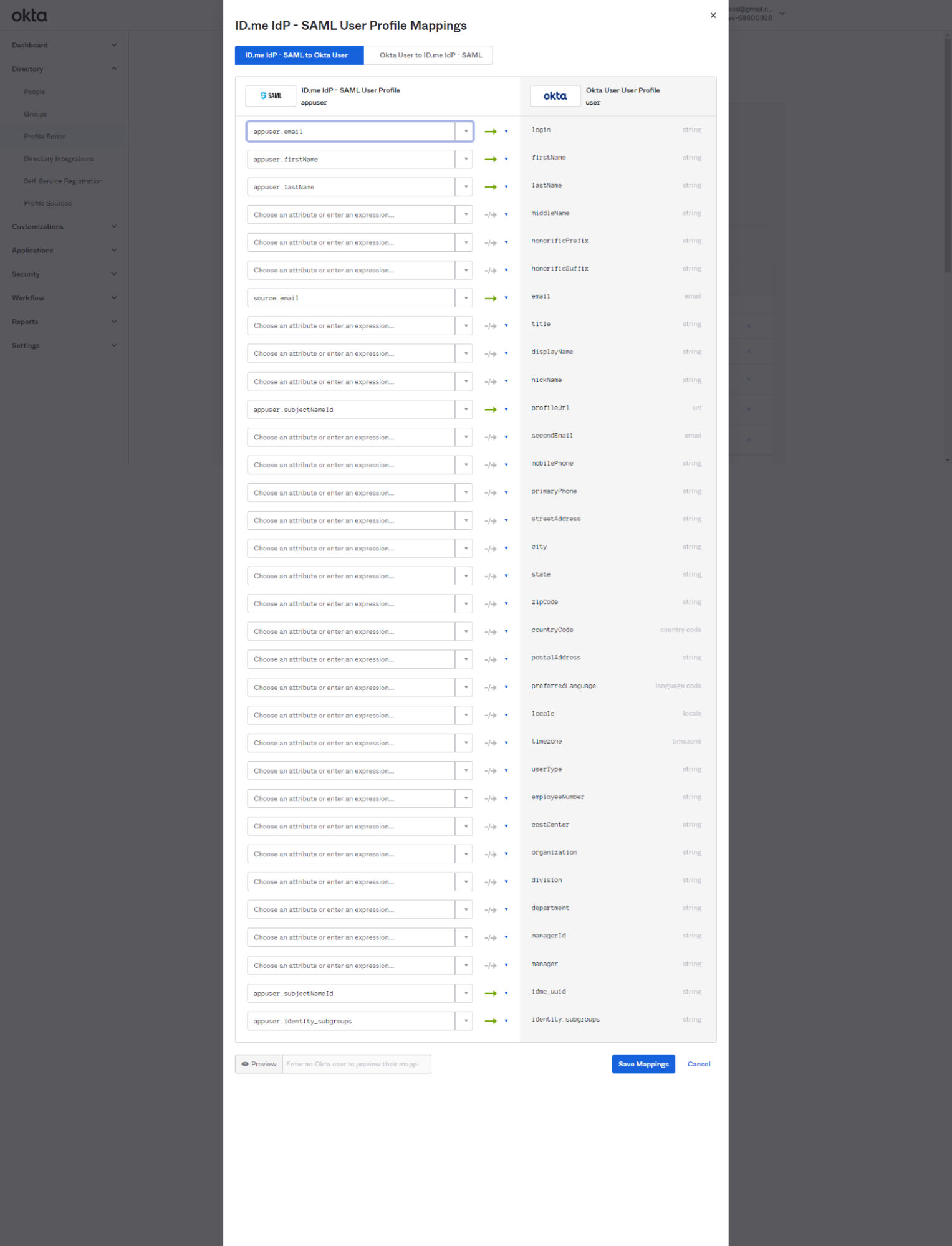
Configure attribute mappings
Configure ID.me
This portion of the configuration is completed by an ID.me Solution Consultant. You will need to provide the following information to complete the setup:
Okta Metadata
Provide the metadata file from your Okta Identity Provider configuration. You can download this by navigating to Security > Identity Providers, expanding the ID.me IdP - SAML actions, and selecting Download metadata.
Okta Audience URI
The Entity ID for your Okta tenant.
Assertion Consumer Service (ACS) URL
The URL where ID.me should send the SAML response.
Signing/Encryption Certificate
The X.509 certificate from your Okta metadata, used for verifying signatures and encrypting assertions.
Test the integration
Select Create Rule and Activate
This configuration will require all users to sign in via ID.me when accessing your Okta tenant. You can configure rules to apply only to specific applications, groups, or users if preferred.