PingOne OIDC integration guide
Overview
This guide provides steps to integrate PingOne with ID.me using the OpenID Connect (OIDC) protocol.
Intended audience
Developers and IAM administrators responsible for configuring federation between PingOne and ID.me.
What you will build
A federated authentication flow where PingOne delegates user authentication to ID.me.
Result
A federated OIDC authentication flow where PingOne delegates authentication to ID.me.
Identity proofing behavior
ID.me policy configurations drive authentication behavior, identity verification settings, and returned attributes.
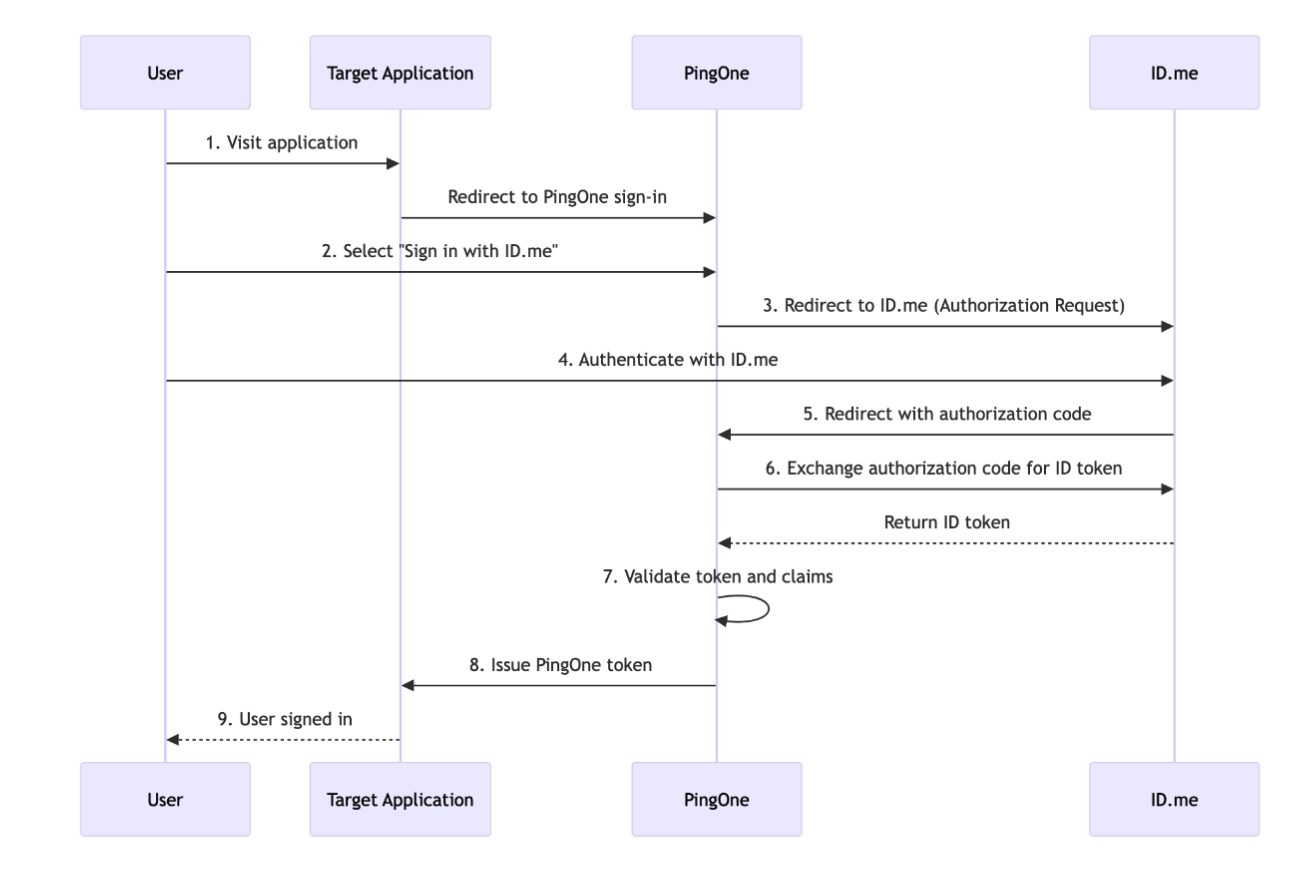
Authentication flow
The following steps outline the OIDC authentication flow between the user, PingOne, and ID.me:
Prerequisites
- Active PingOne customer solution environment
- Access to PingOne with administrative permissions to manage identity providers, authentication policies, and application configurations
- An ID.me sandbox account for testing your integration
- Understanding of OIDC flows and terminology
- An application to test the sign-in flow
Environments
ID.me provides two environments:
api.idmelabs.com
api.id.me
Examples
- OIDC issuer (Sandbox):
https://api.idmelabs.com/oidc - OIDC issuer (Production):
https://api.id.me/oidc - SAML metadata URL (Sandbox):
https://api.idmelabs.com/saml/metadata - SAML metadata URL (Production):
https://api.id.me/saml/metadata
Configure PingOne
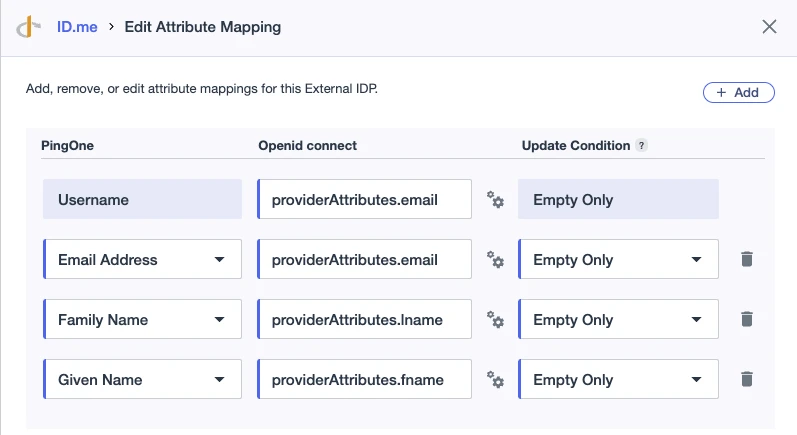
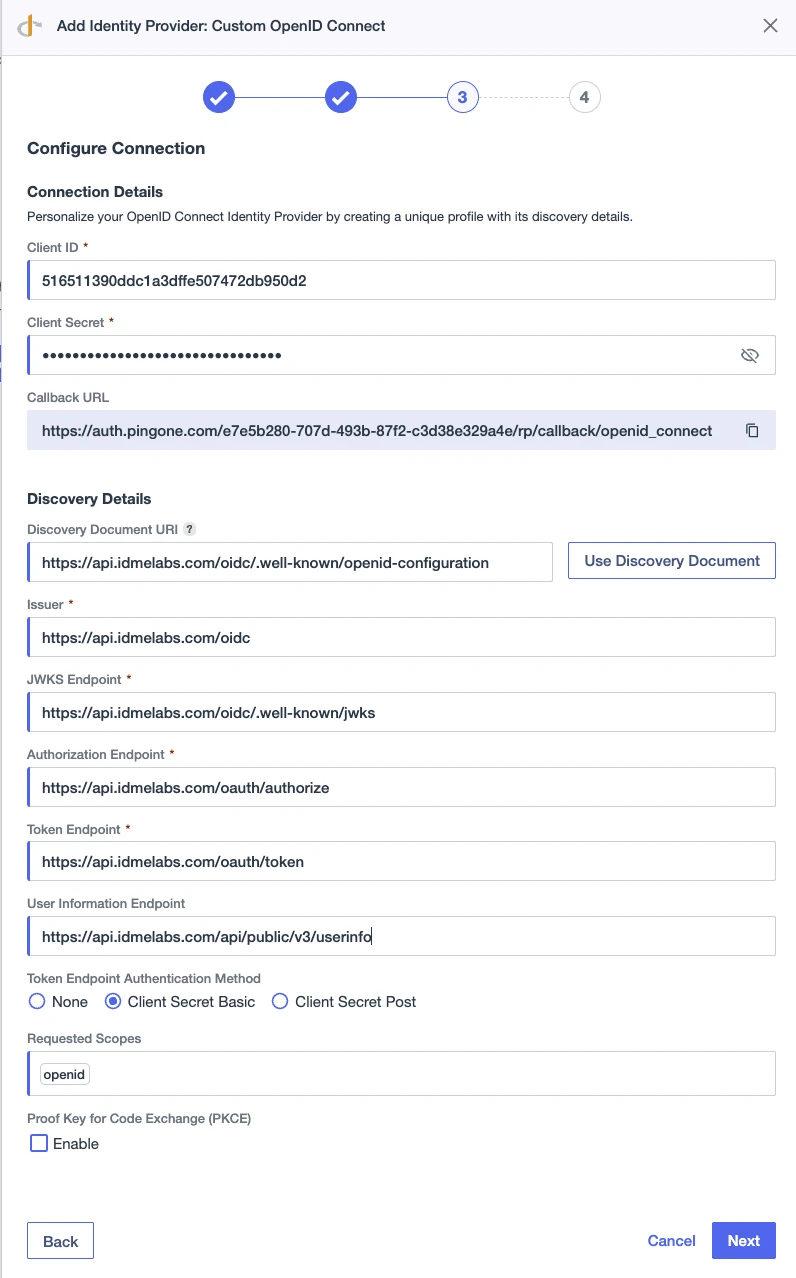
Configure ID.me as an OIDC External IdP
Add the Sign in with ID.me button by selecting Upload Custom Image and uploading the ID.me logo
You would not use this button to test the flow in this guide, but it is good practice to add this when possible for future use cases.
Configure the connection using the Client ID and Client Secret provided by your ID.me Solution Consultant
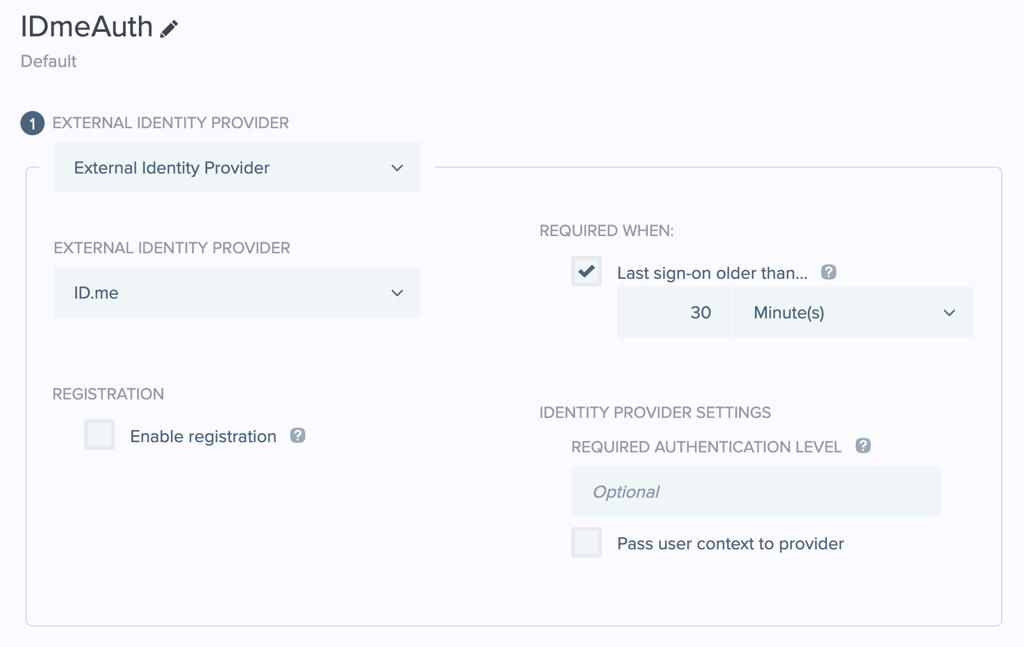
Configure authentication policies
Define the RP/SP configurations within your application
Configure ID.me
This portion of the configuration is completed by an ID.me Solution Consultant. You will need to provide the following information to complete the setup:
Redirect URIs
The Redirect URI for your PingOne External Identity Provider. This is typically generated by PingOne after creating the provider.
Policy handle name
Confirm the ID.me policy handle (e.g., ial2 or teacher).
Test the integration
You can test the integration by constructing an authorization URL with the appropriate ACR values to signal required assurance levels.